Data Breaches Are Not a Bug. They're the Architecture.
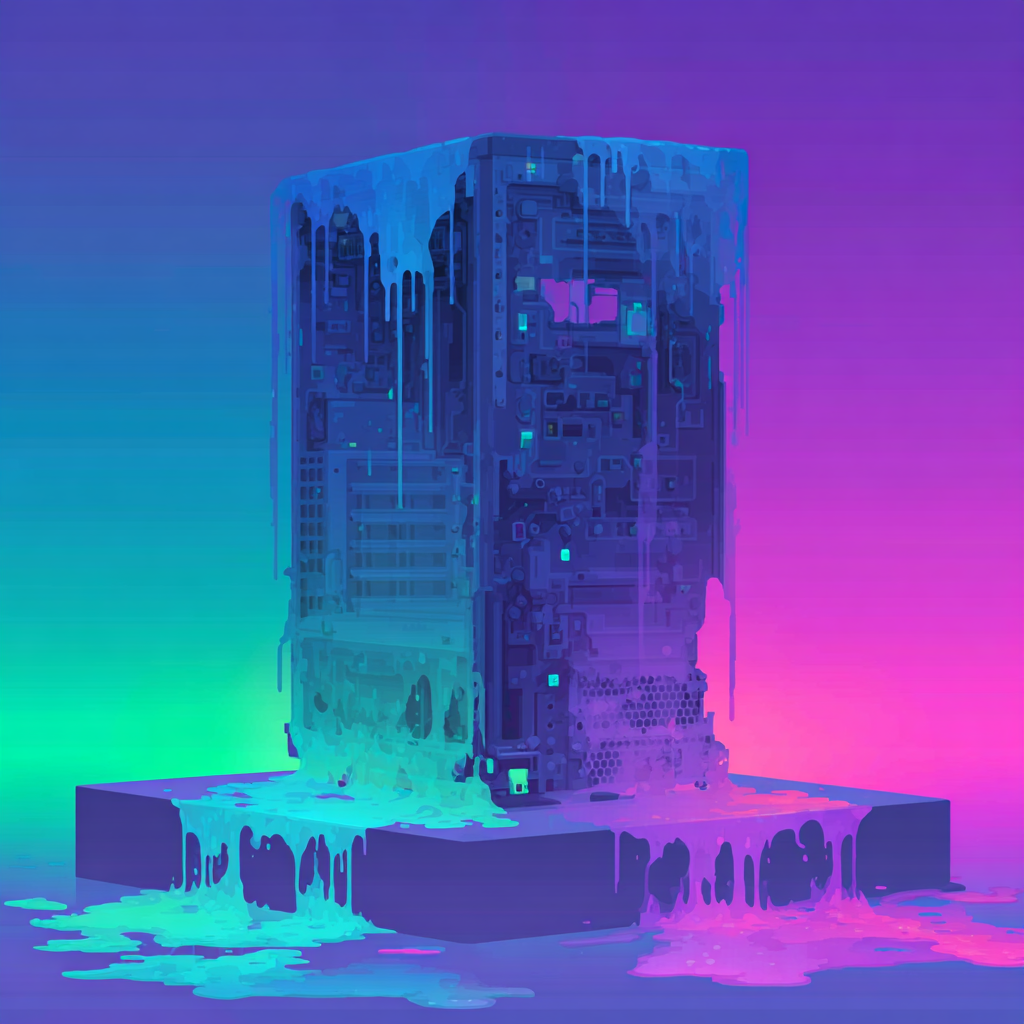
Every organization today operates as a centralized vault of personal data. Names, addresses, passport numbers, financial records—all sitting in a single database, waiting to be stolen.
The cost is staggering: billions of records exposed annually, destroyed trust, regulatory fines, and permanent identity damage for millions. The traditional approach of "protecting the fortress walls" has failed.